Questions Q2-1.
To make the communication bidirectional, each layer needs to be able to provide two opposite tasks, one in each direction.
Q2-2.
The link-layer switch is normally involved in the first two layers of the TCP/ IP protocol suite: a. the physical layer, b. and the data-link layer.
Q2-3.
The router is involved in: a. three physical layers, b. three data-link layers, c. and only one network layer.
Q2-4.
The identical objects are the two messages: one sent and one received.
Q2-5. a. At the application layer, the unit of data is a message. b. At the network layer, the unit of data is a datagram. c. At the data-link layer, the unit of data is a frame. Q2-6.
A frame is a link-layer data unit. It encapsulates a data unit coming from the network layer. In this case, the data unit is a datagram.
Q2-7.
A user datagram is a transport-layer data unit. It decapsulates a data unit going to the application layer. In this case, the data unit is a message.
Q2-8.
The data unit should belong to layer 4. In this case, it is a user datagram.
1
2 Q2-9.
We mentioned HTTP, FTP, SMTP, SNMP, TELNET, SSH, and DNS.
Q2-10. The transport-layer packet needs to include two port numbers: source and destination port numbers. The transport-layer header needs to be at least 32 bits (four bytes) long, but we will see in Chapter 24 that the header size is normally much longer because we need to include other pieces of information. Q2-11. a. At the application layer, we normally use a name to define the destinationcomputer name and the name of the file we need to access. An example is [email protected] b. At the network layer, we use two logical addresses (source and destination) to define the source and destination computers. These addresses are unique universally. c. At the data-link layer, we use two link-layer addresses (source and destination) to define the source and destination connections to the link. Q2-12. The answer is no. Multiplexing/demultiplexing at the transport layer does not mean combining several upper-layer packets (from the same or different applications) into one transport-layer packet. It only means that each of the transport-layer protocols (such as TCP or UDP) can carry a packet from any application-layer protocol that needs its service. However, a transport-layer packet can carry one, and only one, packet from an application-layer protocol. For example, UDP can carry a message from FTP in one user datagram and a message from HTTP in another user datagram. Q2-13. The application layer is the top layer in the suite; it does not provide services to any layer, which means multiplexing/demultiplexing does not exist for this layer. Q2-14. We do not need a link-layer switch because the communication in this case is automatically one-to-one. A link-layer switch is needed when we need to change a one-to-many communication to a one-to-one. Q2-15. We do not need a router in this case because a router is needed when there is more than one path between the two hosts; the router is responsible for choosing the best path at each moment.
Problems P2-1.
The services provided in part a and part b are the opposite of each other.
3 a. Layer 1 takes the ciphertext from layer 2, inserts (encapsulates) it in an envelope and sends it. b. Layer 1 receives the mail, removes (decapsulates) the ciphertext from the envelope and delivers it to layer 2. P2-2.
The services provided in part a and part b are the opposite of each other. a. Layer 2 takes the plaintext from layer 3, encrypts it, and delivers it to layer 1. b. Layer 2 takes the ciphertext from layer 1, decrypts it, and delivers it to layer 3.
P2-3.
In 10 years, the number of hosts becomes about six times (1.2010 ≈ 6.19) the number in 2010. This means the number of hosts connected to the Internet is more than three billion.
P2-4.
The system transmits 150 bytes for a 100-byte message. The efficiency is 100/ 150 or 66.66%.
P2-5.
The advantage of using large packets is less overhead. When using large packets, the number of packets to be sent for a huge file becomes small. Since we are adding three headers to each packet, we are sending fewer extra bytes than in the case in which the number of packets is large. The disadvantage manifests itself when a packet is lost or corrupted during the transmission; we need to resend a large amount of data.
P2-6. a. The network layer is responsible for route determination. b. The physical layer is the only layer that is connected to the transmission media. c. The application layer provides services for the end users. P2-7. a. User datagrams are created at the transport layer. b. The data-link layer is responsible for handling frames between adjacent nodes. c. The physical layer is responsible for transforming bits to electromagnetic signals. P2-8.
There should be an upper-layer identifier in the header of the IP protocol to define to which upper-layer protocol the encapsulated packet belongs. The identifier is called the protocol field (See Figure 19.2 in Chapter 19).
4 P2-9.
The following shows the situation. If we think about multiplexing as many-toone and demultiplexing as one-to-many, we have demultiplexing at the source node and multiplexing at the destination node in the data-link layer. However, some purists call these two inverse multiplexing and inverse demultiplexing.
FTP
HTTP
DNS
L1
FTP
UDP
Multiplexing TCP Demultiplexing
SNMP
DNS
IP
L3
a. At the source node
L1
SNMP
UDP Demultiplexing
TCP
IP
L2
HTTP
L2
Multiplexing
L3
b. At the destination node
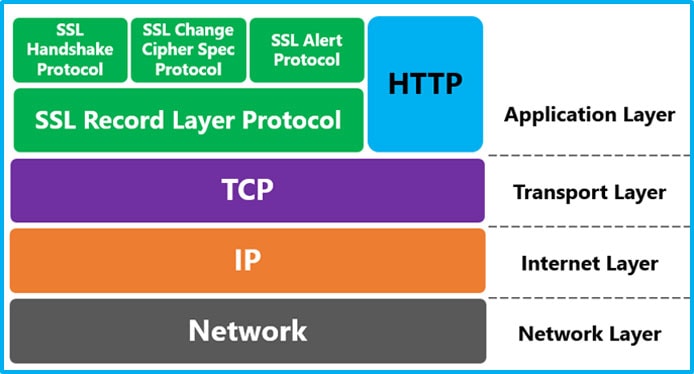
P2-10. Every time any packet at any layer is encapsulated inside another packet at the same layer, we can think of this as a new layer being added under that layer. The following shows the new suite.
Application Security Transport
Application Security Transport
Network
Network
Link
Link
Physical
Physical
P2-11. The following shows the layers. Note that we have not shown the security checking that you need to pass through because it does not have the counterpart when you arrive. It must be included in baggage/checking layer.
Source/destination airport
Source/destination airport
Baggage checking/claiming
Baggage checking/claiming
Boarding/unboarding
Boarding/unboarding
Takeoff/Landing
Takeoff/Landing
Flying
5 P2-12. The following shows the position of the presentation layer. The new layer is at the same position as the presentation layer in the OSI model if we ignore the session layer.
Application
Application
Presentation Transport Network Data link Physical
New layer
Presentation Transport Network Data link Physical
P2-13. The only two layers that need to be changed are the data-link layer and the physical layer. The new hardware and software need to be installed in all host, routers, and link-layer switches. As long as the new data-link layer can encapsulate and decapsulate datagrams from the network layer, there is no need to change any protocol in the upper three layers. This is one of the characteristics of the protocol layering. P2-14. The reason for having several protocols in a layer is to provide different services to the upper-layer protocols. The services provided by UDP are different from the services provided by TCP. When we write an application program, we need to first define which transport-layer protocol is supposed to give services to this application program. Note that this does not violate the principle of layer independence. The independency of a layer means that we can change a protocol in a layer as long as the new one gives the same services as the old one. This does not mean that we can replace UDP by TCP, because they provide different services. P2-15. The following shows the layers and the flow of data. Note that each host is involved in five layers, each switch in two layers, and each router in three layers.
East coast office
West coast office Point-to-point WAN
R1
R2
Router
Router
5
5
4
4
3 2
2
1
1
Host
Switch
3
3
3
3
3
2
2
2
2
2 2
2
2
1
1
1
1
1 1
1
1
Router
Router
Switch
Host
- Forouzan Tcp Ip Protocol Suite Pdf Reader
- Forouzan Tcp Ip Protocol Suite Pdf File
- Tcp Ip Protocol Suite Forouzan Pdf
- Forouzan Tcp Ip Protocol Suite Pdf Download
Slides for 『TCP/IP Protocol Suite』 4th Ed.
Communication and networking by behrouz a forouzan may 2nd 2018 search pdf books com behrouz a forouzan data communication and networking tata mcgraw hill. The internet and tcp ip protocol suite technologies related to data communication and networking may be the fastest growing in todays culture data communications.
Part 1Introduction and Underlying Technologies
Tcp Ip Protocol Suite Forouzan 3rd Edition Pdf Free Download 12 - DOWNLOAD 19ed66dd5a Amazon.in - Buy TCP/IP Protocol Suite (Mcgraw-hill Forouzan Networking) book online at best prices in India on Amazon.in.tcmd 756a key, tcpip protocol suite 4th edition pdf, bs hack 2012, kari wurher 3gp sex video ska4at besplatno, tcmania gold edition ver 10 skin, tcpip forouzan torrent.Home Data. TCP IP Protocol Suite 4th Ed. Download 1 file. SINGLE PAGE PROCESSED JP2 ZIP download. Download 1 file.
Chapter 1. Introduction
Chapter 2. The OSI Model and TCP/IP Protocol Suite, ProtocolOverviewExample
Chapter 3. Underlying Technologies
Part 2Network Layer
Chapter 4. Introduction to Network Layer
Chapter 5. IPv4 Addresses
Chapter 6. Delivery and Forwarding of IP Packets
Chapter 7. Internet Protocol Version 4 (IPv4)
Chapter 8. Adress Resolution Protocol (ARP)
Chapter 9. Internet Control Message Protocol (ICMPv4)
Chapter 10. Mobile IP
Chapter 11. Unicast Routing Protocols (RIP, OSPF, and BGP):Routing Supplement, OSPFsample
Chapter 12. Multicasting and Multicast Routing Protocols:McastTrees, MOSPFsample, MOSPFhandout
Part 3Transport Layer
Chapter 13. Introduction to Transport Layer

Chapter 14. User Datagram Protocol (UDP)
Chapter 15. Transmission Control Protocol (TCP)
Chapter 16. Stream Control Transmission Protocol (SCTP)
Part 4Application Layer
Chapter 17. Introduction to Application Layer
Chapter 18. Host Configuration: DHCP
Chapter 19. Domain Name System (DNS)
Chapter 20. Remote Login: TELNET and SSH
Chapter 21. File Transfer: FTP and TFTP
Chapter 22. World Wide Web and HTTP
Chapter 23. Electronic Mail: SMTP, POP, IMAP, and MIMEIP over ATM
Chapter 24. Network Management: SNMP
Chapter 25. Multimedia
Forouzan Tcp Ip Protocol Suite Pdf Reader
Part 5Next Generation
Chapter 26.IPv6 Addressing
Chapter 27. IPv6 Protocol
Forouzan Tcp Ip Protocol Suite Pdf File
Chapter 28. ICMPv6
Part 6Security
Tcp Ip Protocol Suite Forouzan Pdf
Chapter 29. Cryptography and Network Security
Forouzan Tcp Ip Protocol Suite Pdf Download
Chapter 30. Internet Security
